Replicate Kubernetes Ingress on Docker Compose stack
Exposing a container service to the outside is often not easy. Especially when considering the SSL certifications. To address this problem, Kubernetes introduced a concept called Ingress, which provides routing from the outside of the cluster to services within the container[1].
Traditionally, there are mainly three methods of exposing the service to the internet. The simplest way is to expose the port to the host directly, then it will be able to access via <hostip>:<port>. Another method is to use a reverse proxy on the host, mapping the services with a domain. The last is similar to the second but instead, deploys the reverse proxy using another container.
The second method is basically the extension of the first method. The last method, however, should be recommended since it uses the container's hostname for addressing. Which adds more flexibility.
In this article, we will introduce a method similar to the last method mentioned above but includes some GUI tools for easier management.
Nginx Proxy Manager (npm but not)
NPM provides functionalities such as proxying the services, acquiring Letsencrypt certifications automatically, etc. We are going to use this service to mimic the Kubernetes Ingress.
After installation, if by following the setup guide, the service will be available under port 81.
It should be noted that NPM doesn't support MySQL version 8.x. A workaround for this is to use SQLite as the database.
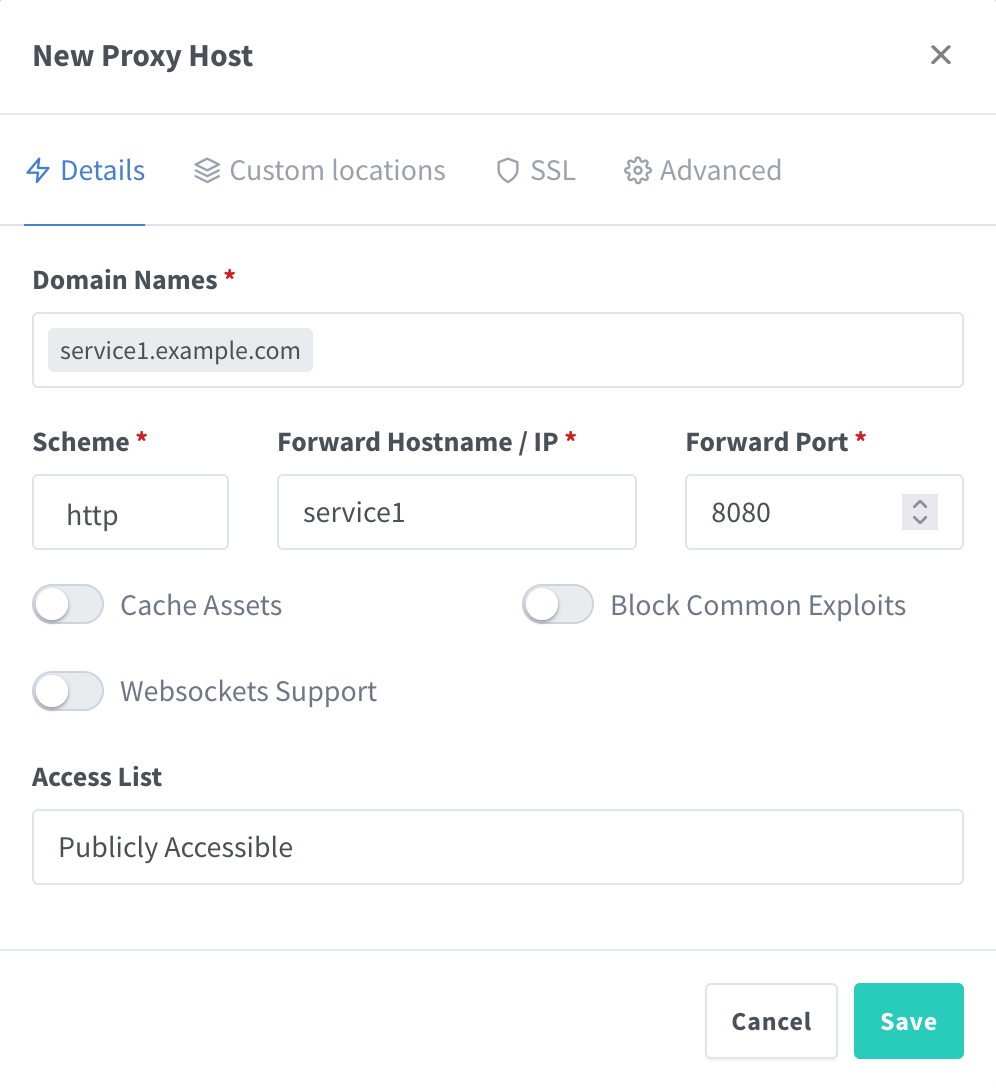
Proxying the service
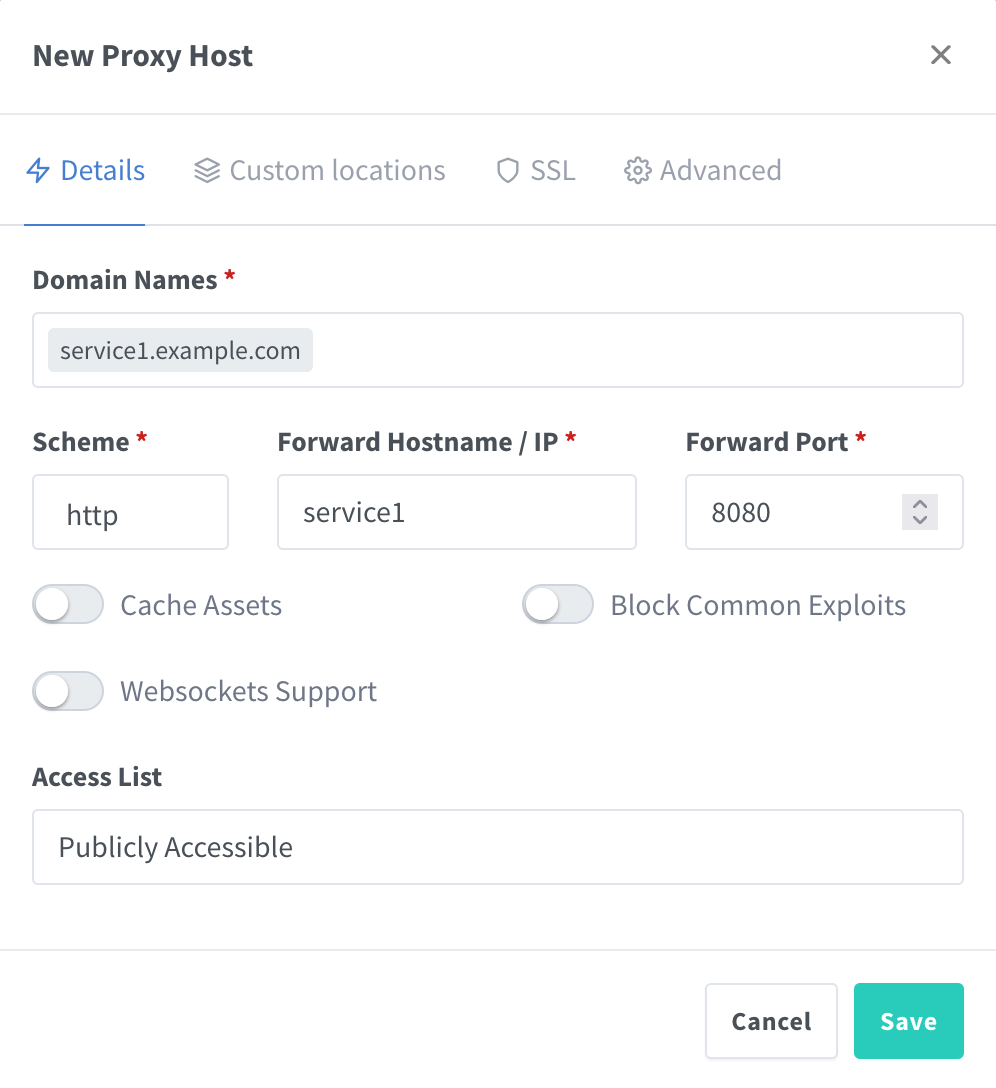
The configuration is rather simple, given the example above. SSL certifications could be enabled from the SSL tab. With options of uploading certification manually or acquiring new certification from Letsencrypt. This should be useful for exposing the service to the public.